Seamless S3 encryption does not imply better security
SSE-S3 helps to tick a box, but nothing else

Encryption
Especially in small companies, I see an excessive emphasis on encryption. Semi-technical people, usually mid-management, ask the question "Is the data encrypted?" and draw conclusions from a simple "yes". Granted, secure systems usually employ some form of encryption so a "no" answer would suggest that there is room for improvement. But assuming adequate security from the fact that the data is encrypted is a logical error.
Encryption is just one tool in a toolbox to improve security. It opens up ways to store data securely in an untrusted place, and also to have finer access control. But the mere fact of encryption does not make something more secure. It just allows for more control.
There is even an example when encryption makes thing worse. Encrypting passwords instead of hashing them weakens your stance after a breach. Why is that? Encryption means reversibility, and that property is not needed for passwords. Even worse, if the key is also leaked during a breach, all the passwords will be in plain text. That can not happen with proper hashing.

One AWS service, the SSE-S3 (Server-Side Encryption for S3) is a role model for encryption that is really hard to see what improvements it makes. But it ticks the box of encryption just fine.
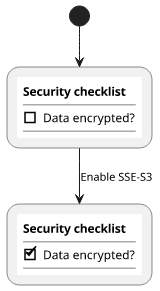
Seamless encryption
What makes encryption seamless? It is when all you need to do is to enable it (if it is not enabled by default). For example, you are reading this blog via HTTPS which is an encrypted connection without having to do anything to use it. You get all the benefits of encryption without lifting a finger.
But this is in-flight encryption, let's see what kind of seamless encryption S3 offers!

AWS stores your objects on hard drives which may or may not be encrypted. SSE-S3 promises to enforce strong encryption without any friction. Look the docs:
Server-side encryption protects data at rest. Amazon S3 encrypts each object with a unique key. As an additional safeguard, it encrypts the key itself with a master key that it rotates regularly. Amazon S3 server-side encryption uses one of the strongest block ciphers available, 256-bit Advanced Encryption Standard (AES-256), to encrypt your data.
It sounds ultra-secure, right? I bet no hacker could steal any of your objects if you use this.
Access control
Let's see what it protects from! Encryption in the cloud is all about access control, as you usually don't have access to the encrypted files.
What do you need to download the object? You need access via IAM or bucket policies:

Seems familiar?
Yes, it is exactly the same as the unencrypted version:
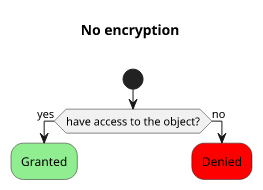
No matter how strong the encryption is or even if it's enabled or not if someone has access to the object he can download it. Seamlessly.
What are the benefits?
So what exactly seamless encryption protects from?
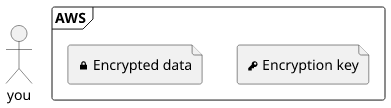
It is encryption at-rest, which means if somebody has access to the underlying drives or some lower-level component then it makes a difference.
Cloud security courses usually start with the notion of the shared responsibility model. In a nutshell, it means you are responsible for the security of your account but you can trust the cloud provider that the controls it provides work.

If you leave the bucket open to the world and got hacked, the blame is yours. But you can be sure that the bucket/IAM policies can not be bypassed by other means.

Where does it lead us?
If you trust AWS that it takes good care of the data then it does not matter if it's encrypted or not. Maybe the data is already stored in encrypted drives, maybe not.
But if you don't trust the cloud provider then you can't be sure that it won't use the encryption key to steal your data. The only real attack vector is a low-level rogue employee who has access to the hardware but not the encryption.
But let's reverse the argument for a moment! If this is really that easy as to turn a switch on, why not use it? Treat it as the default, just don't assume that your data is any more secure than without it.
The real benefit
So, what is the real benefit of SSE-S3?