NixOS
Nix
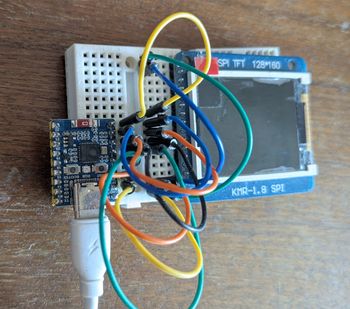
NixOS first impressions: writing system-level tests
Continue reading →
 Tamás Sallai
Tamás Sallai
 Tamás Sallai
Tamás Sallai
May 25, 2026